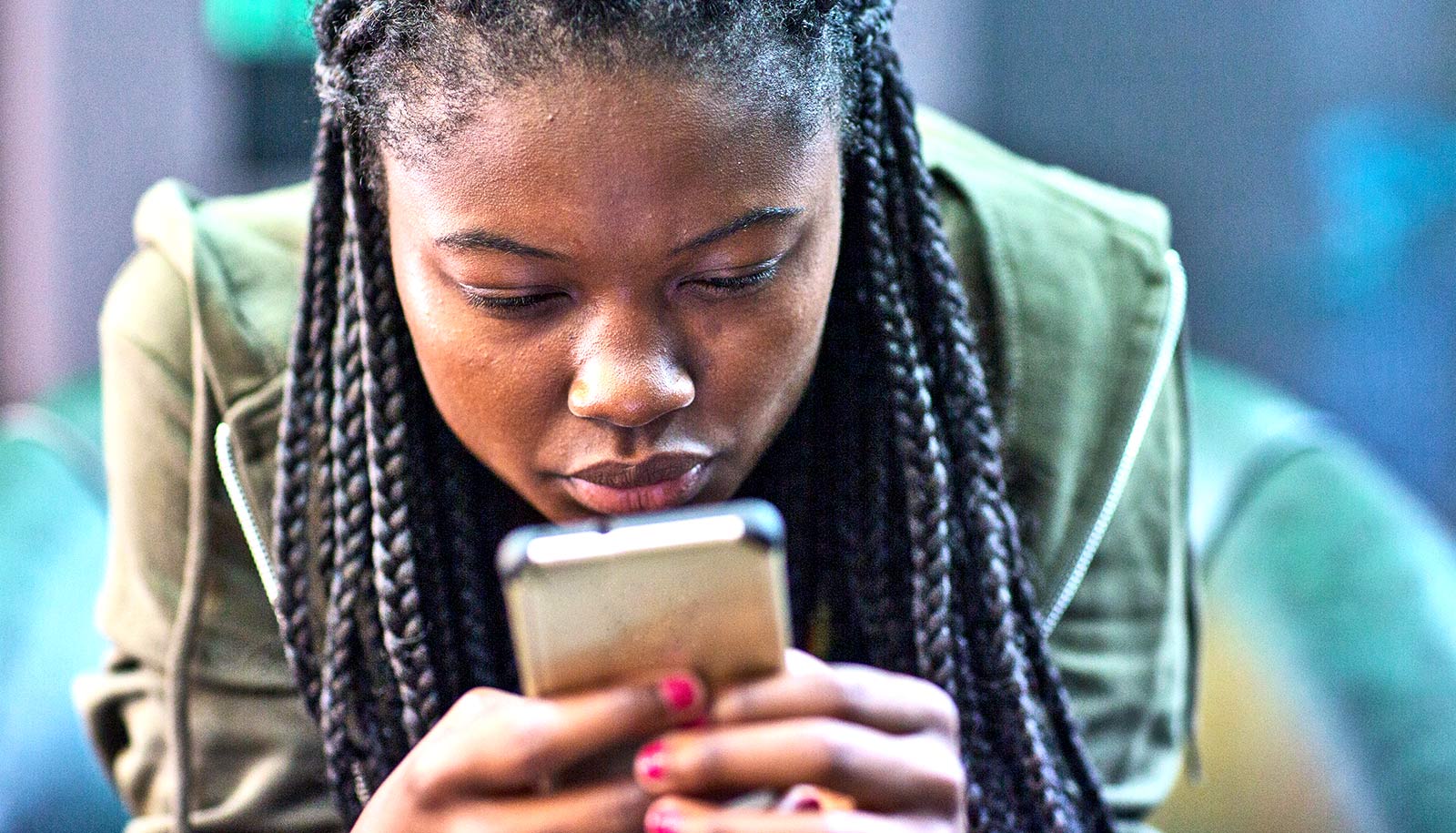
Oversharing on social media threatens your online security, warns Dan Lin.
“We cannot go out and socialize during this pandemic, so people are turning to social media to share what is going on with their lives,” says Lin, an associate professor of electrical engineering and computer science, and director of the I-Privacy Laboratory at the College of Engineering at the University of Missouri. “But it can be risky.”
Before a person decides to play along with the latest social media challenge, or post a picture of their family home, Lin says to consider the following three things:
1. Games are no joke
Online games that challenge people to answer a few questions about themselves, or post an image, seem innocent enough. But these games can often extract sensitive information about a person, such as their first job, their first car, or their mother’s maiden name—all of which can give hackers answers to commonly used security questions used on other websites such as online banking.
Lin notes two recent challenges as opportunities for hackers to steal a person’s information. Recently, social media users were posting their senior photos as a way to support the Class of 2020. But hackers can use those photos to gain the name of a person’s high school and graduation year.
Additionally, social media users were sharing photos of their mothers for Mother’s Day. But those images could put a person’s mother at risk by revealing identifiable information and provide clues as to whether the mother lives alone.
“If you want to celebrate with your mother, talking to her is better than sharing her picture with strangers,” Lin says.
2. Beware of what you share
Images you take with digital cameras contain metadata that can provide information about the photo, such as where and when it was taken. While many social media platforms automatically remove that information when a photo is posted online, Lin warns that publishing images without first deleting the metadata can provide hackers with information a person did not intend to share, such as the GPS location of the place that the photo was taken.
She suggests removing metadata by opening the photo file and deleting this information, or using existing metadata removal software.
Lin says people also should be aware of what is present in the background of their photos. She suggests avoiding posting images that show a house number, vehicle, or unique decorative household items that can help hackers locate a person. It can also reveal personal information that a person may not want to have shared in the public realm.
3. Check your privacy settings
While privacy settings from social media providers have improved over the last several years, it’s still easy for hackers to bypass that security, Lin says. Even if a person has blocked someone from seeing their information, another user connected with that person can save their information and pass it along to people outside of their connections—sometimes without their knowledge.
Therefore, Lin says if a person does not want something to be publicly seen by everyone, including strangers, it’s best not to share it at all.
Can AI boost social media security?
Lin is currently doing research on how artificial intelligence can help social media providers offer more advanced levels of privacy.
One strategy involves predicting what type of photo people are posting and alert the user to how other people may use that image. For instance, if someone wants to share an image with a select group of friends, the system could warn the user that friends of those friends could still view their photo, including people they intentionally excluded from the group.
A second strategy would allow social media channels to automatically recommend privacy protections for a particular image based on the type of photo and past user behavior. A family photo, for instance, could come with automatic privacy settings blocking others from sharing or downloading it. However, a funny picture of a pet might come with fewer security recommendations.
A more advanced method involves facial replacement in group photos. Rather than blurring out someone’s face in a photo of a class or public setting, which draws the attention of a hacker, this method allows social media providers to replace a person’s likeness with a synthetic facial image based on the person’s privacy needs obtained from his or her past behavior. The change would be subtle enough that those looking at the photo would not be able to tell it had been altered, Lin says.
Ultimately, Lin says it’s up to social media companies to determine whether to implement new security strategies. Until then, people should be cautious about what they choose to post on social media. Anything posted online never fully disappears—even if you delete it immediately.
Source: University of Missouri